Latest News
Read all latest blog posts
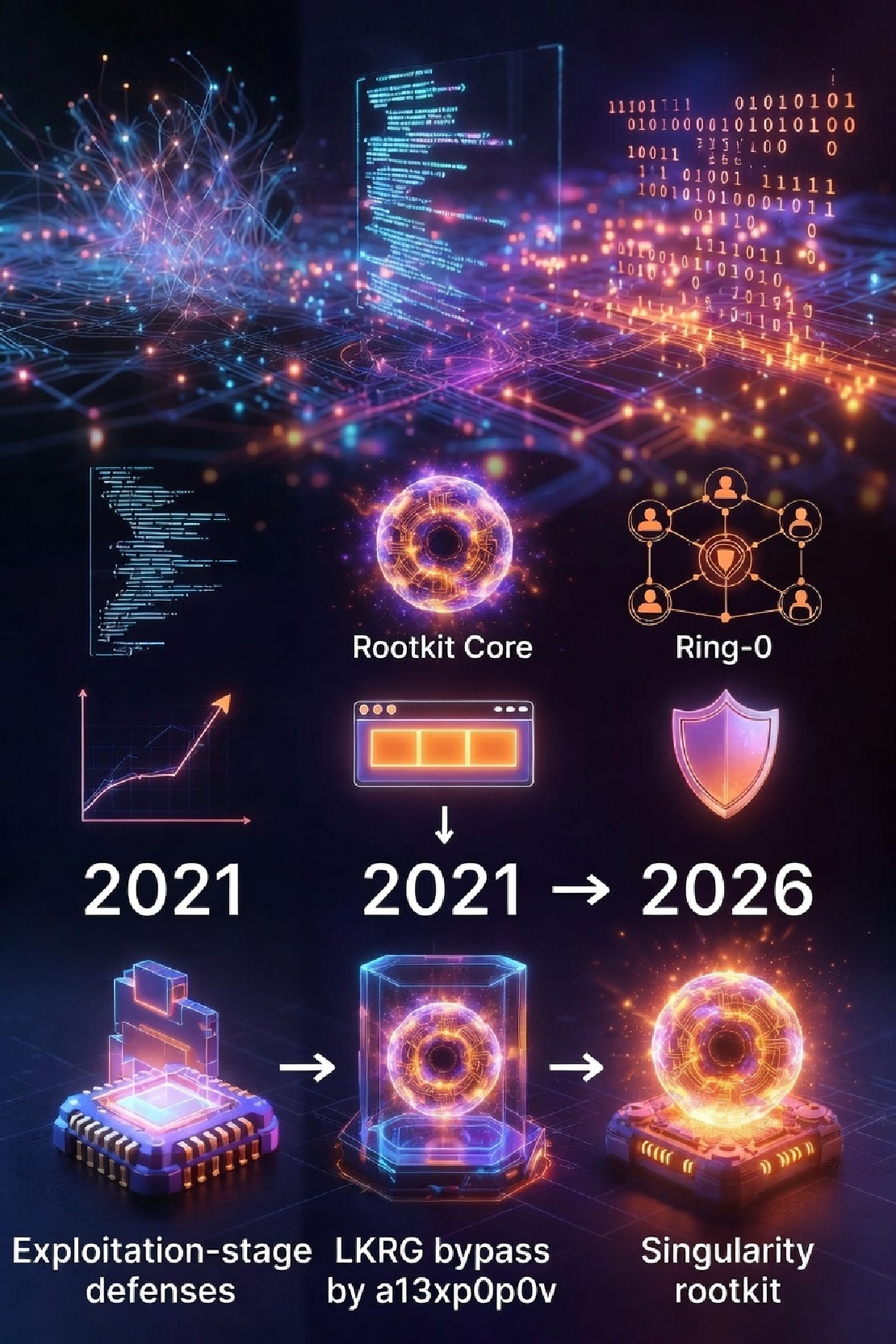
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier Singularity is currently one of the most highly engineered rootkits.
Read More
xz/liblzma Backdoor: Open Source Nuke? Maybe Not That Bad!
xz/liblzma Backdoor: Open Source Nuke? Maybe Not That Bad! Story Background On March 29, 2024, a report exposing a backdoor in the upstream source code of the controversial open-source project, the xz software package, was made public on the oss-security mailing list.
Read More
Supermicro x11ssh-F OpenBMC Porting (WIP)
Supermicro x11ssh-F OpenBMC Porting (WIP) Introduction to BMC and OpenBMC BMC, short for Baseboard Management Controller, is a specialized microcontroller embedded in certain computers, typically servers.
Read More
Key management of OpenPGP Card
Key management of OpenPGP Card Background As blank smartcards supporting Java Card 3.
Read More
Protect the Watcher: Hardened SIEM/XDR server with VED
Background Modern cybersecurity operation centers significantly depend on two key elements: agent-based security solutions operating on desktops, laptops, and server operating systems, and a threat analysis system, often referred to as a Security Information and Event Management (SIEM) system or eXtended Detection and Response (XDR).
Read More
Vault Range - The Measure and Resilience of Weaponized Exploit Methods for Linux
Disclaimer VED (Vault Exploit Defense) test image contains only the VED kernel module, and does not contain any security baselines, access control policies and situational hardening solution.
Read More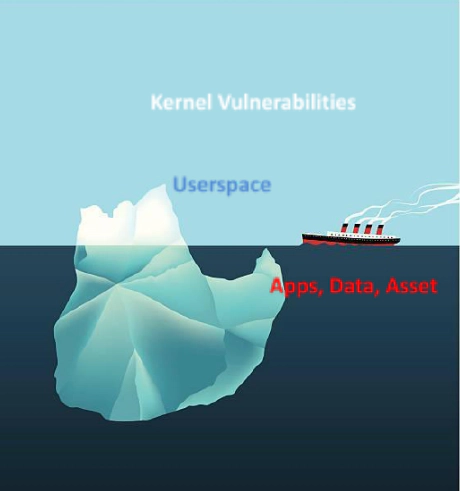
+PROTECTING LINUX AT KERNEL LEVEL WHY AND HOW
Introduction We designed Vault Exploits Defense (VED) as a foundation security layer for various flavors of Linux operating system.
Read More
Memory corruption in JCRE: An unpatchable HSM may swallow your private key
Background The key has always been a core target of security protection.
Read More
Avoiding Single-Point-of-Failure and securing the Root Infrastructure: TCG TPM 2.0
What is TCG TPM 2.0? Trusted Computing Group (TCG) Trusted Platform Module (TPM) 2.
Read More
Demystifiying SMPC (Secure multi-party computation) and its threat model
Prologue SMPC is an interesting topic, whose the applications include systematic security and cryptographic engineering, and this article will discuss its principles, threat models and use-case.
Read More