Welcome to HardenedVault
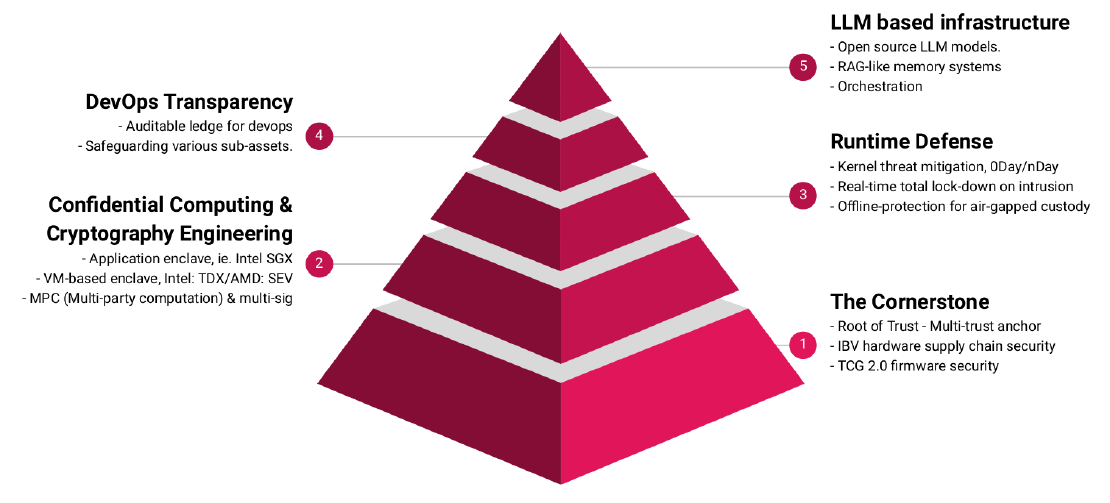
HardenedVault is a leading security firm offering professional consulting services focused on OS and below-OS security. With nearly a decade of experience in developing advanced system-level security technologies, HardenedVault ensures a robust chain-of-trust from hardware-anchored boot processes through firmware, operating systems, and applications. Our approach not only meets rigorous compliance and regulatory standards but also integrates cutting-edge mitigation techniques and access control measures. This comprehensive security strategy delivers defense-in-depth across various environments, from embedded system to OCP server assets—providing resilient defenses against both known and emerging threats.
Who we are?
Our technical team are a group of old-school hackers, cypherpunks, and stubborn engineers while our management team are originaly from Top 500 C-Level veterans who have spent decades tweaking around interesting things in their respective fields until 2021 when we felt we could do more for the industry, so here we are now.
Our mission
Thanks for visiting the our website. If you’re still reading, it’s likely that you’re a person who is not happy about the current situation of the technology industry. Our vision is simple: to help users build their own Cyber Bunker at the infrastructure level. Achieving this goal requires high performance, security and transparency (open source) that takes into account the industry compliance, as well as decentralization (it’s federated protocol actually) in communications. If you share our philosophical idea, please work with us to make it.