Latest News
Read all latest blog posts
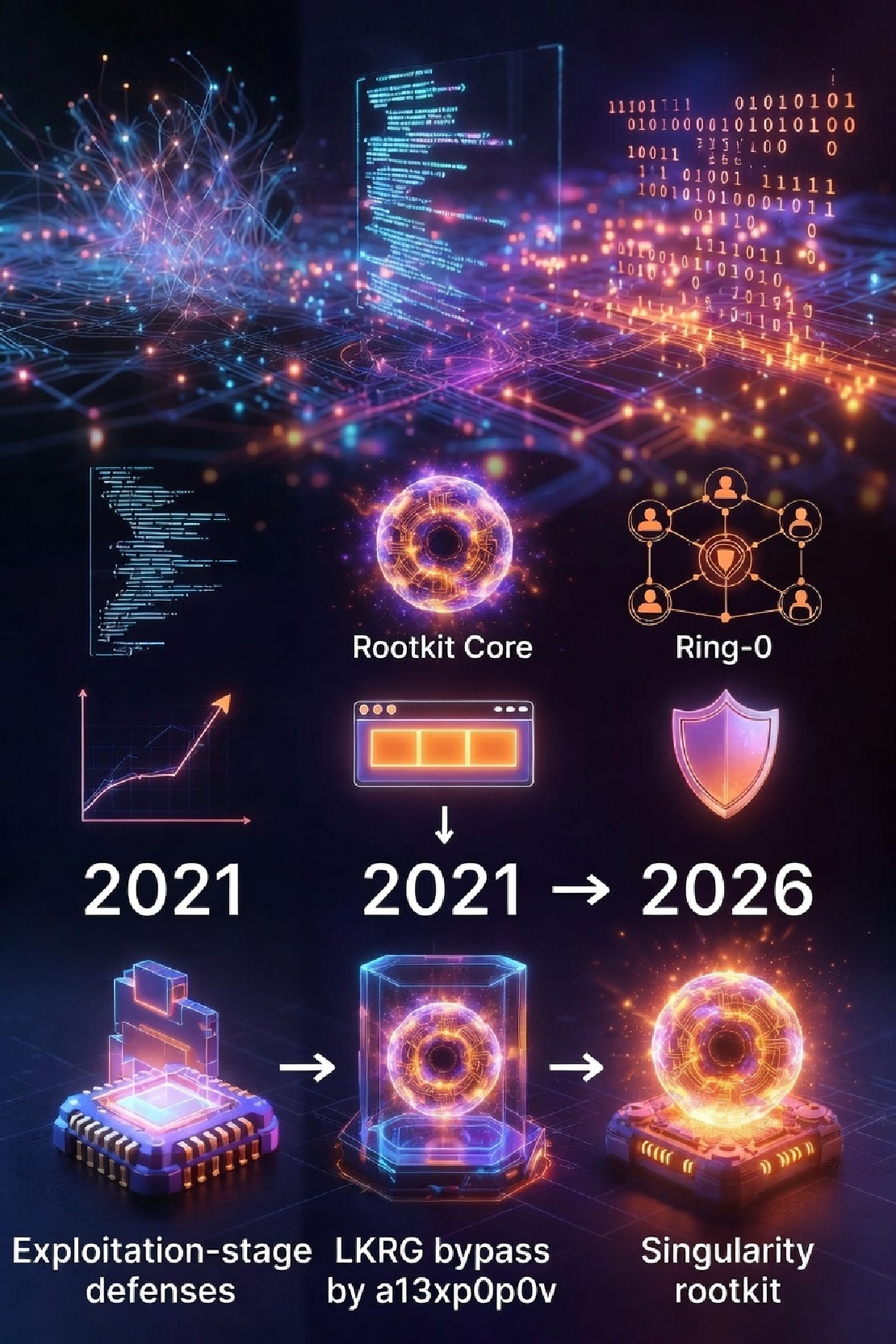
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier Singularity is currently one of the most highly engineered rootkits.
Read More
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier Singularity is currently one of the most highly engineered rootkits.
Read More
VED 2026: after CFI - data only
after CFI - data only The exploitation techniques and mitigation has been evolving rapidly since the paper “Smash the Stack for Fun and Profit” released in Phrack Issue 49.
Read More
HOWTO: build ATF (Trusted Firmware ARM) and OPTEE for RK3588
HOWTO: build ATF (Trusted Firmware ARM) and OPTEE for RK3588 To better implement the protection of digital assets in embedded systems, we have chosen the RK3588 as the prototype platform.
Read More
OpenBMC Remote OS Deployment: A Simplified Approach
OpenBMC Remote OS Deployment: A Simplified Approach Many BMC implementations can accept a disk image and present it as a read-only USB mass storage device inserted into the host machine, allowing the host machine to boot from this “disk” for remote installation of the operating system or maintenance tasks.
Read More
SimpleX low-level protocol analysis
Background The SimpleX Chat Protocol is utilized by SimpleX Chat clients for message exchange.
Read More
A Survey of deterministic approach RFC6979 for open source implementations: Mbed-TLS, GnuTLS and OpenSSL
Background The original implementation of DSA-type signature algorithms (including ECDSA) requires a random number that belongs to the same type of mathematical object as the private key (an element of GF(p), where p is a prime number).
Read More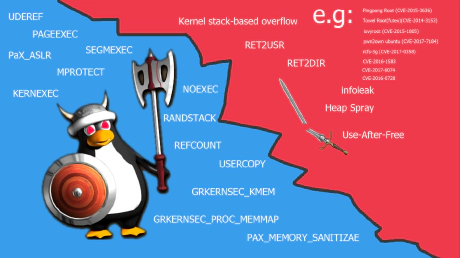
SLUBStick risk assessment for embedded systems
SLUBStick risk assessment for embedded systems The Linux kernel is susceptible to memory safety vulnerabilities due to its size and complexity.
Read More
NBD: A Powerful Tool for data center
NBD: A Powerful Tool for data center NBD, the abbreviation for Network Block Device (protocol), is a protocol that was initially implemented in the Linux kernel version 2.
Read More
Demystifying SFTP
Introduction SFTP is an auxiliary protocol of SSH that allows file transfer between two hosts over the SSH protocol.
Read More