Protect the Watcher: Hardened SIEM/XDR server with VED
Background
Modern cybersecurity operation centers significantly depend on two key elements: agent-based security solutions operating on desktops, laptops, and server operating systems, and a threat analysis system, often referred to as a Security Information and Event Management (SIEM) system or eXtended Detection and Response (XDR). However, the cybersecurity industry grapples with two primary challenges.
First, the majority of security solutions fail to provide comprehensive threat detection at the operating system (OS) and below-OS levels, leaving this crucial area exposed to potential attacks. Second, the threat analysis system often lacks robust protection in alignment with the best security practices, which can inadvertently lead to security breaches.
In response to these challenges, we’ve developed an solution based on an open-source SIEM/XDR Wazuh to demonstrate how we can do about it. This tool integrates seamlessly with VED to extend the monitoring dimension to Linux kernel runtime, along with other security measures, such as CIS compliance, offering a robust solution to the identified threats. Currently, Hardened SIEM/XDR is available on AWS for easy integration and deployment. For those interested in implementing a similar solution in on-premise environments, we’re more than willing to assist. Please feel free to reach out to us for more information on how our solution can enhance your cybersecurity measures.
Tutorial
Wazuh server
To subscribe and boot a Hardened SIEM/XDR server on AWS, follow these steps:
- Log in to your AWS account and navigate to the AWS Marketplace.
- Search for “Hardened SIEM/XDR” in the search bar and select the desired product from the results.
- Click on the “Subscribe” button to subscribe to the product.
- Once the subscription is successful, you will be redirected to the product’s details page.
- On the product details page, click on the “Launch” button to launch the Hardened SIEM/XDR server.
- In the “Configure Instance Details” section, select the desired configuration options for your server, such as instance type, operating system, and security group.
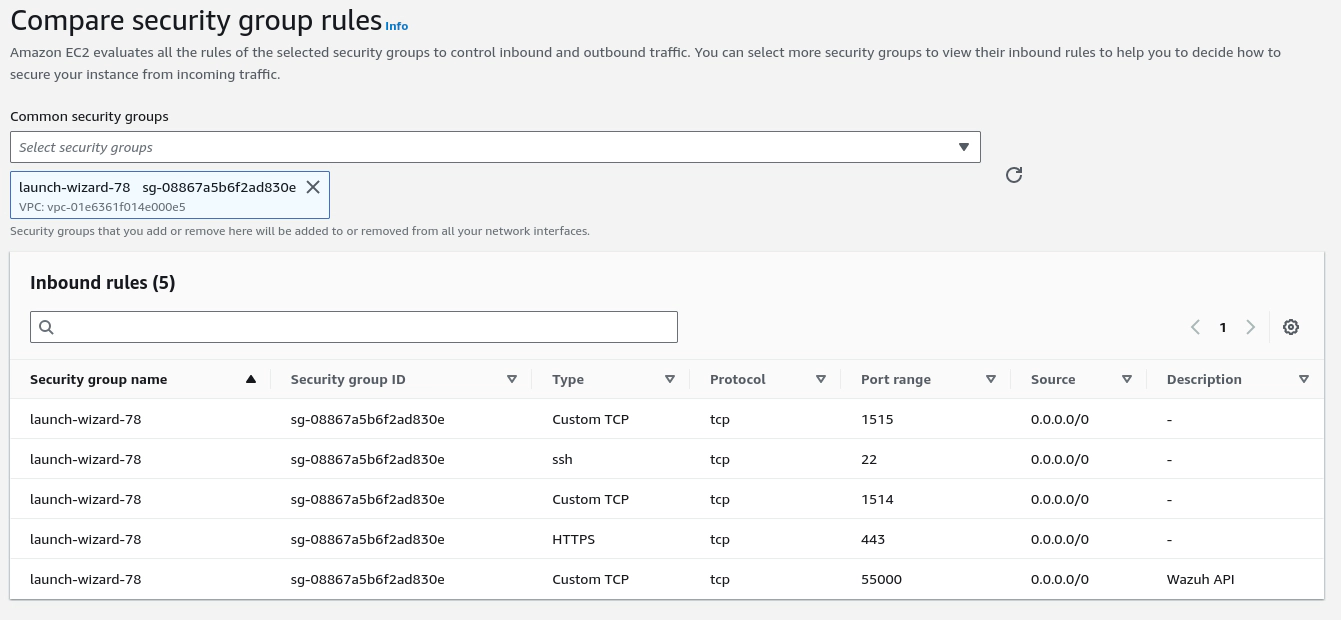
- In the “Security Group” section, select the security group that you want to use for your server. Make sure that the security group allows inbound traffic on the necessary ports for the Hardened SIEM/XDR server:
- Click on the “Launch” button to launch the server.
- Once the server is up and running, you can connect to it using an SSH client or a web browser.
You can get the initial password of Wazuh server by login in the system via SSH.
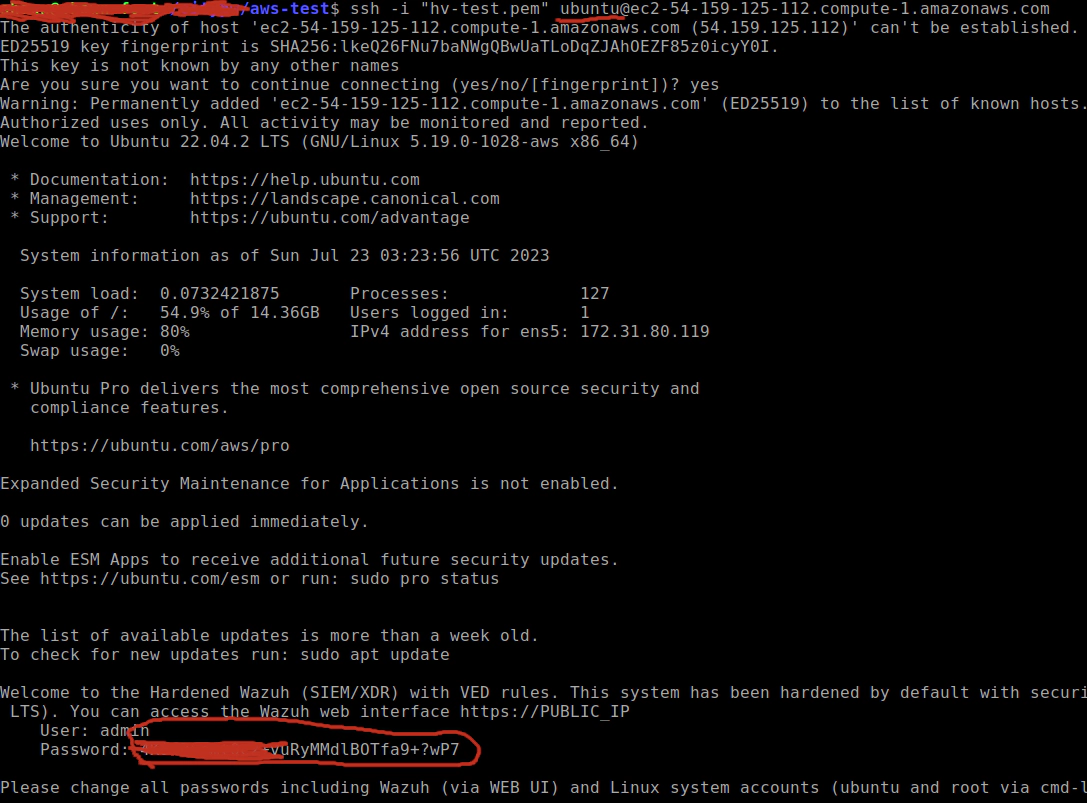
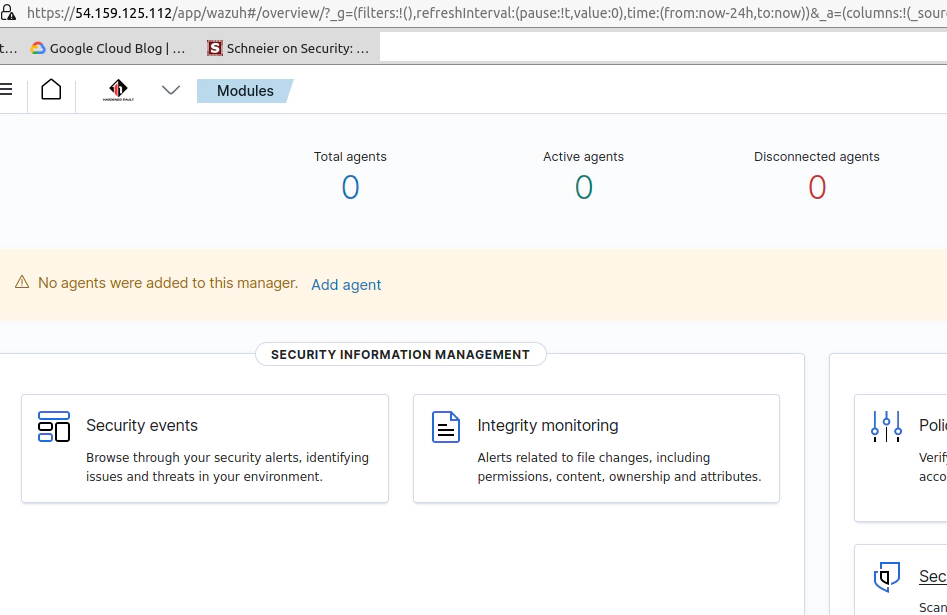
Then you can use the user/password to access the Wazuh WEB UI by web browsers (Firefox/Chromium/etc).
Agent
Boot a server and deploy the Wazuh agent:
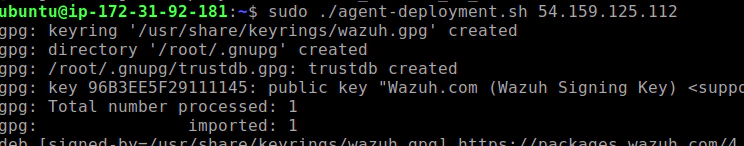
Wazuh server
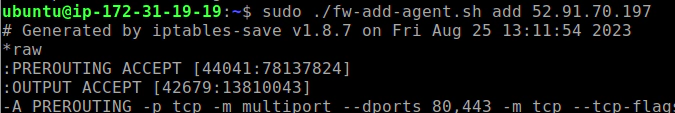
Please keepd this in mind: You need to add each agent’s IP into firewall’s whitelist because it’s an effective measure to protect the server.
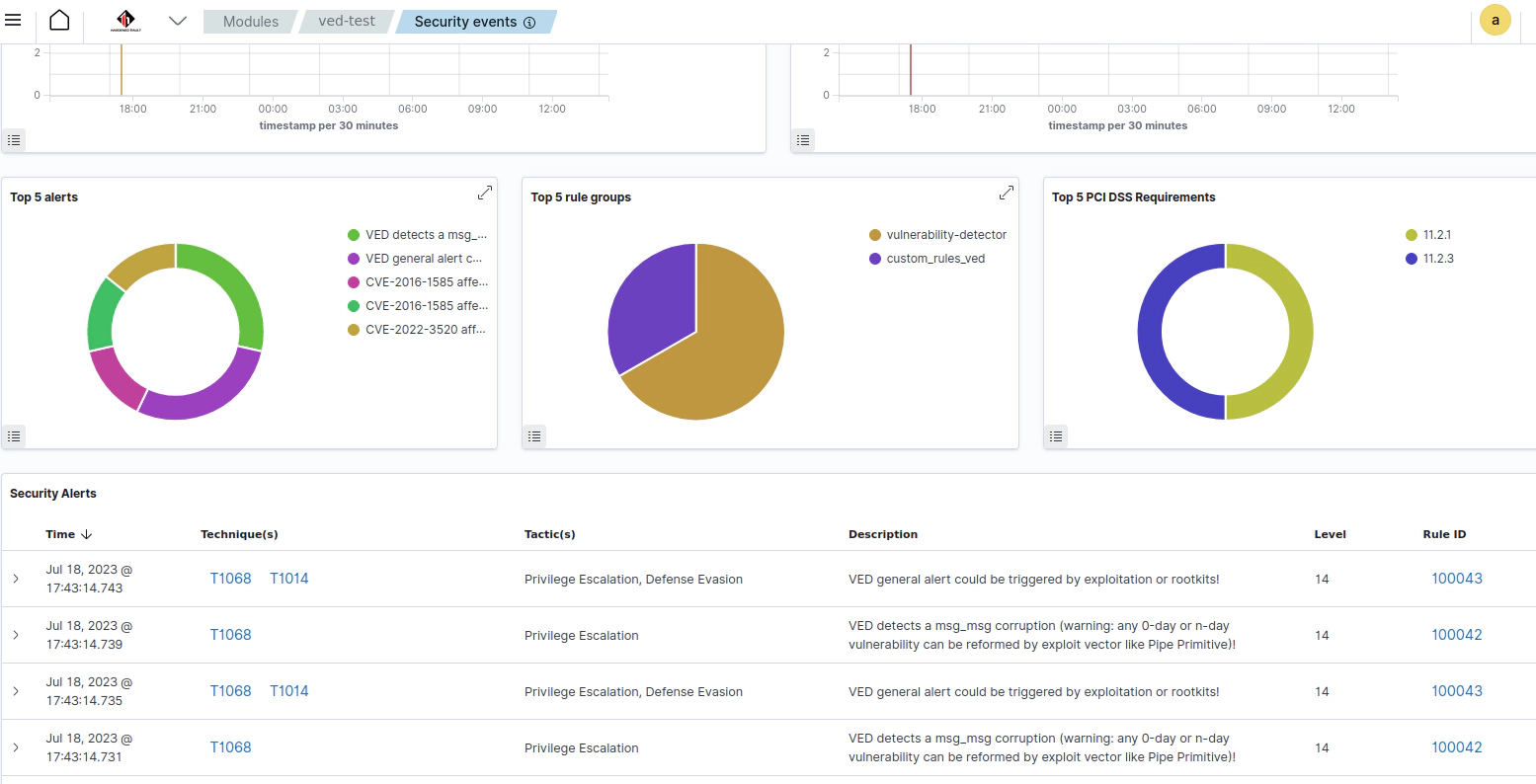
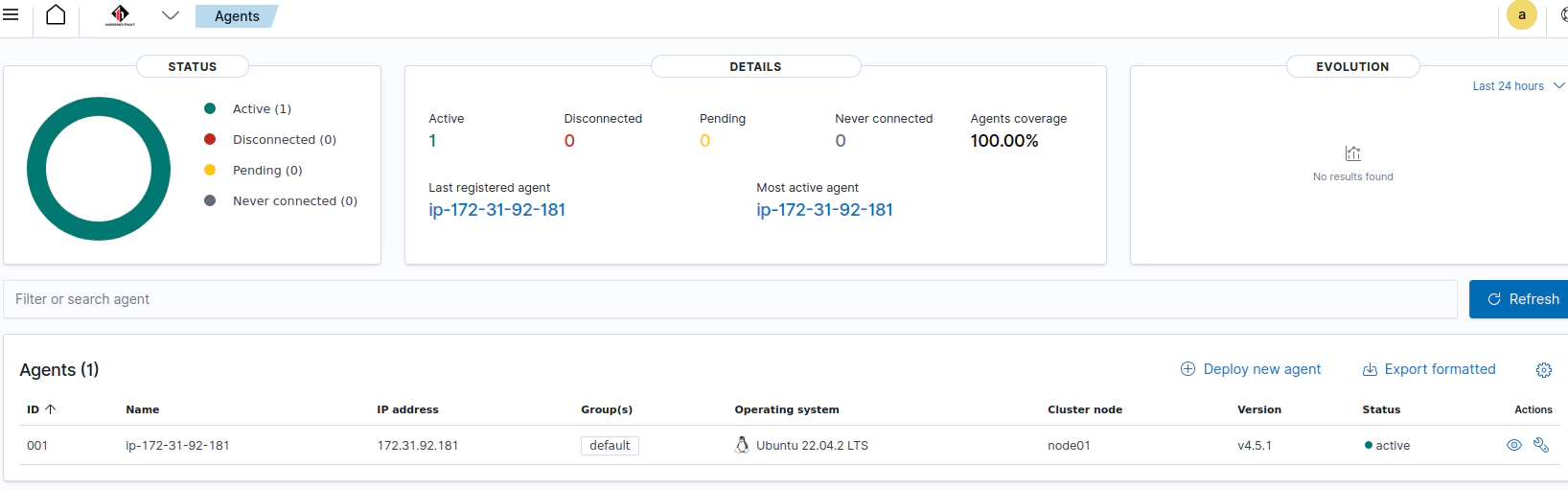
Wait for 30 seconds or so, then you should see the agent’s status via the Web UI:
VED’s capability to extend the monitoring dimension of SIEM/XDR to Linux kernel runtime against privilege escalation, container escape, and rootkits is a powerful enhancement. By incorporating this functionality, VED can provide comprehensive visibility and detection for potential security threats within the kernel. This ensures proactive defense and strengthens the overall security posture of the system, safeguarding against sophisticated attacks and unauthorized access attempts.