Latest News
Read all latest blog posts
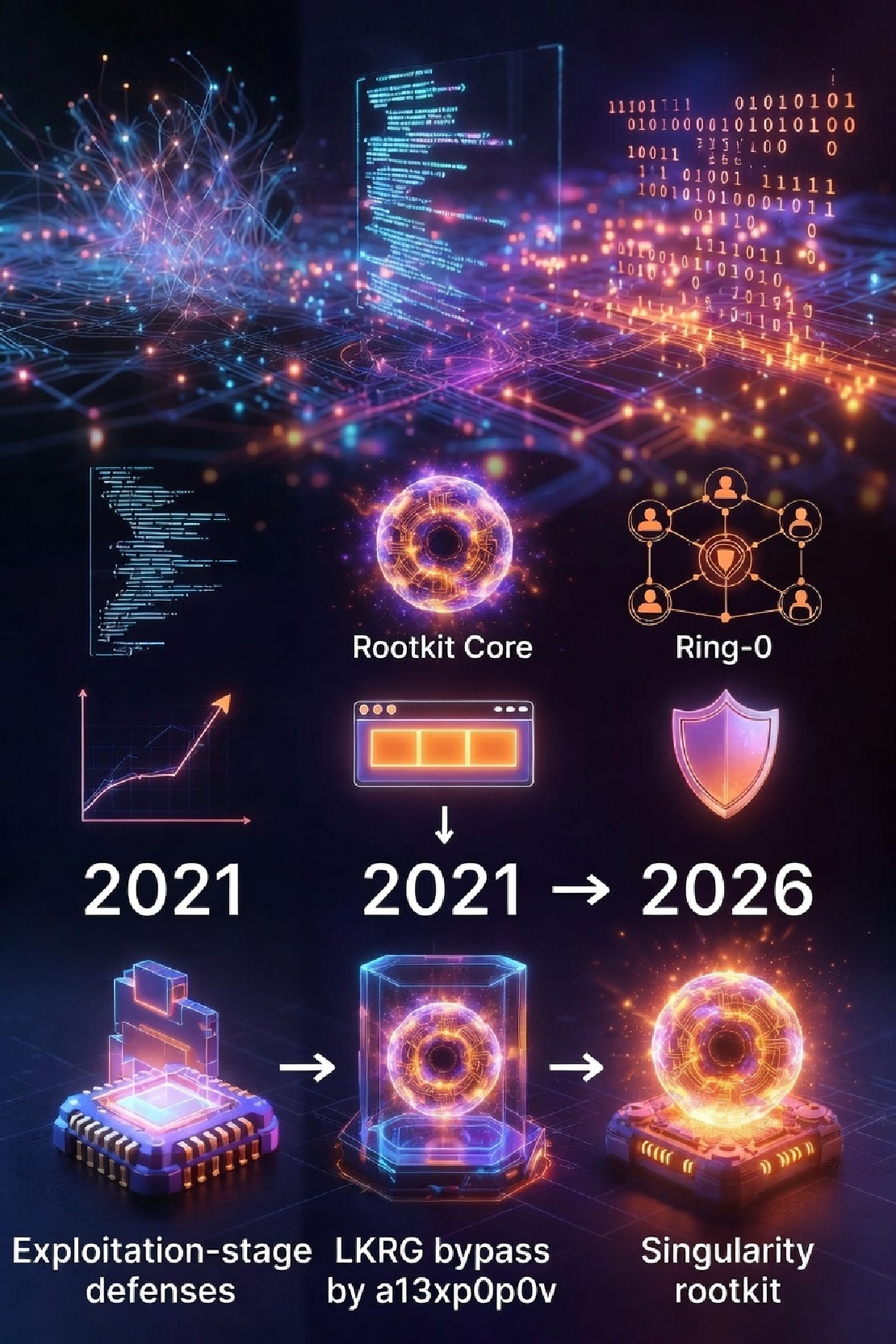
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier
Beyond Cat-and-Mouse: From 2021 (a13xp0p0v) to 2026 (Singularity) — Exploitation Stage Is the Only Real Frontier Singularity is currently one of the most highly engineered rootkits.
Read More
Exploiting CVE-2021-26708 (Linux kernel) with sshd
Kernel vulnerability CVE-2021-26708 Alexander Popov has published an article Four Bytes of Power: Exploiting CVE-2021-26708 in the Linux kernel which use a four-byte overwrite vulnerability to do privilege escalation.
Read More
Intel SGX deprecation review
The rumors about Intel SGX deprecated in new processors has been confirmed, 12th generation processors (Workstation/Desktop/Laptop/embedded platforms) will deprecate SGX and the SGX will continue to support only in high-end Xeon CPU for server:
Read More
Risk analysis of Log4Shell (CVE-2021-44228) and mitigation
Risk analysis of Log4Shell (CVE-2021-44228) and mitigation Log4Shell is a high impact exploitable bug in Java logging framework logj4.
Read More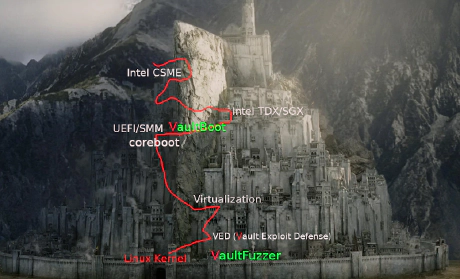
VaultBoot: Next-Gen Firmware Security Solution
Background Firmware is a special type of software, mainly used for the control and communication of the underlying hardware.
Read More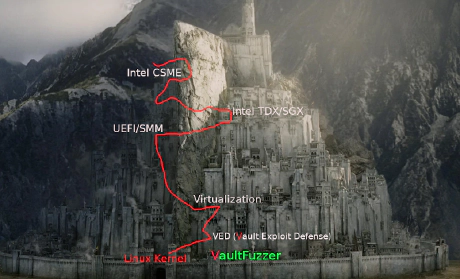
VaultFuzzer: A state-based approach for Linux kernel
Background Since the beginning of computer software development, software quality has become an inevitable issue in the field of software testing.
Read More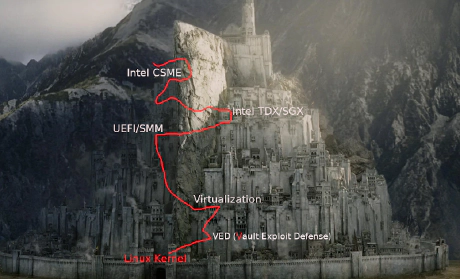
VED (Vault Exploit Defense): A threat detection and prevention system
Background In the beginning of the hacker's era, a long-term battle for control of the “CORE” in memory has been waged since Aleph One published the paper Smashing The Stack For Fun And Profit on Phrack Issue 49 in 1996.
Read More
What every CISO and security engineer should know about Intel CSME
Background The majority of infosec community are trying to ignore the risks below the OS in past decades but it’s impossible to bury all of them at low cost today.
Read More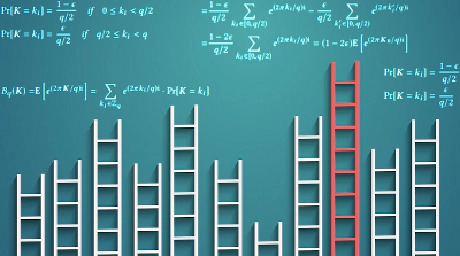
VaultHSM report: The way to confirm whether the Smart Card (J3H145) supports RFC-6979 ECDSA implementation
Background The original implementation of DSA-type signature algorithm (including ECDSA) needs a random number which belongs to the same mathematical object of the private key (an element of GF(p), in which p is a prime number).
Read More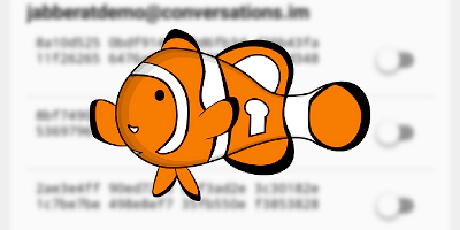
Public crypto audit report: lurch/OMEMO
lurch/OMEMO Security Assessment Crypto is a neutral technology just like the natural existence (“For he makes his sun rise on the evil and on the good, and sends rain on the just and on the unjust.
Read More